86% of #Cyberthreats are concealed in encrypted traffic—and there’s been a 185% surge in encrypted attacks on #Government . Learn how #ZeroTrust architecture can reduce your reliance on legacy technology and strengthen your #Security . FedTech Magazine dy.si/oYErK


ICI Bucharest participated, between April 23-24, 2024, in the conference 'Ideas that change Romania', an event organized by the Commission for European Affairs of the Chamber of Deputies: ici.ro/en/events/ici-…
#cybersecurity #cyberthreats #research #collaboration


Pentesting accounts for an average of 13% of total IT security budgets securitymagazine.com/articles/10058… #Cyberwarfare #Cyberthreats


From #databreaches to ransomware attacks, #cybercrime knows no bounds. Discover how #internalauditors navigate the intricacies of #cyberthreats with their expertise and ensure the resilience of #enterprises . Read more: bit.ly/3WegYhU
#aurex #digitalthreat #security #blog


The New Frontiers Of Cyber #Fraud >> Adapting To The Age Of #AI And #Deepfakes
buff.ly/3Ud5acX
Forbes @DataSoftGroup #business #leadership #regtech #fintech #tech #regulation #compliance #CISO #CIO #CTO #CEO #data #genAI #generativeAI #cybercrime #cyberthreats


SMBs are prime targets for #CyberThreats . Our blog addresses these challenges, emphasizing #CyberSecurity 's importance and providing insights into common threats. We simplify selecting cybersecurity solutions, ensuring effective defense.
Read more: bit.ly/3Rq6ckt



86% of #Cyberthreats are concealed in encrypted traffic—and there’s been a 185% surge in encrypted attacks on #Government . Learn how #ZeroTrust architecture can reduce your reliance on legacy technology and strengthen your #Security . FedTech Magazine dy.si/32nK7S2


#CyberThreats are surging with the digitization of connected cars. Our research emphasizes the importance of managing operational technology (OT) security.
Discover proactive strategies for manufacturers to mitigate these risks. Click here to read more: bit.ly/41M7HhY


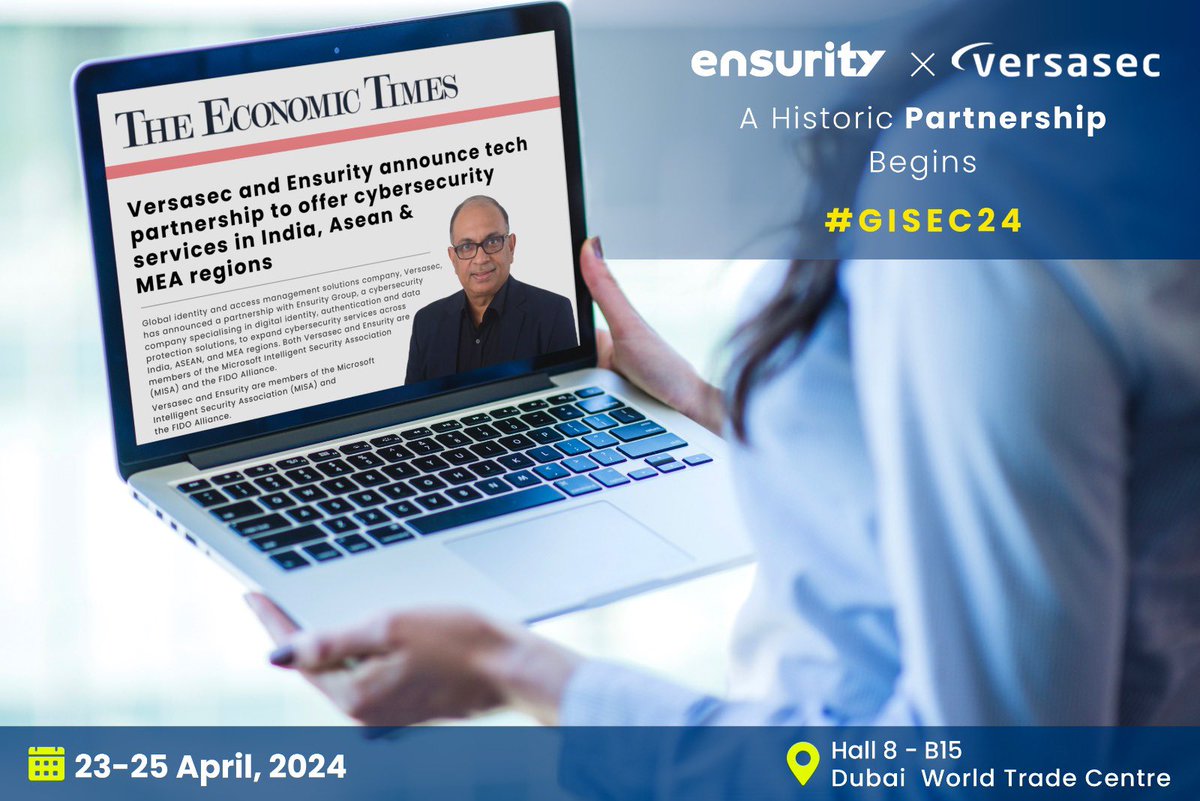
Happy to announce our partnership with Versasec, a global leader in identity and access #managementsolutions ! Together we're empowering organizations to fortify their defenses against evolving #cyberthreats with a customer centric approach and ease of management.

The Cybersecurity #Leadership Handbook for the #CISO and the #CEO
A must-have for anyone interested in learning how a comprehensive, integrated approach to #cybersecurity can help organizations build a robust, adaptive defense against #cyberthreats
buff.ly/41a574n

Hosted by This Week Health, join @RubrikInc and Microsoft to discover how to fortify patient data against #CyberThreats ! This webinar will provide insights from Ryan Baker (Rubrik) and David Houlding (Microsoft) on the latest cybersecurity trends: rbrk.co/4a445dL


86% of #Cyberthreats are concealed in encrypted traffic—and there’s been a 185% surge in encrypted attacks on #Government . Learn how #ZeroTrust architecture can reduce your reliance on legacy technology and strengthen your #Security . FedTech Magazine dy.si/bCBuCE2


Hosted by This Week Health, join @RubrikInc and Microsoft to discover how to fortify patient data against #CyberThreats ! This webinar will provide insights from Ryan Baker (Rubrik) and David Houlding (Microsoft) on the latest cybersecurity trends: rbrk.co/4a445dL


Check out the Top 5 Most Active Threat Actors in Q1 2024 Identified by Threatlynx's Cyber Threat Intelligence Tool!
#cti #cyberthreats #threatactor


#Infosec Tip: regular #antivirus programs can't detect fileless #malware . More about other #CyberThreats : buff.ly/2xXlV2w
#CyberAttack #CyberSecurity #DataProtection #threats #vulnerability


Cyber threats like #ransomware and stealthy #malware are always on the move, making traditional security look like yesterday's news. You don't want to be fighting advanced #cyberthreats with outdated #cybersecurity weapons. Here’s how you can fortify your cyber-defenses and stay



Here Come the #AI Worms
buff.ly/48vJqhK
WIRED #cybercrime #cybercriminals #malware #cyberthreats #cyberattacks #databreaches #ransomware #leaders #leaders hip #management #CISO #CIO #CTO #cybersecurity #security #infosec #ArtificialIntelligence #genAI #generativeAI