Our comprehensive portfolio of #EndpointSecurity solutions defends your workspace against modern threats with an intricate web of layered protection. 🛡️ 🔒
Learn more – read our eBook! 📘: dell.to/416pvUs #DellTrustedWorkspace #DellSecurity

#Infographic :
Here are 10 essential #cybersecurity tips vía Incrux Technologies
#iotsecurity #security #endpointsecurity #hacking #malware #virus #ransomware #DigitalTransformation
#AI #innovation #IoT #Data #Data Science #BigData #Flutter #100DaysOfCode #coding #python #javascript #Bot


It is finally here!!!! Security CoPilot with Microsoft Intune early access program is here! Check out our latest blog: lnkd.in/gu7sJ3wQ
#MSIntune #Intune #EndpointSecurity #SecurityCoPilot


Endpoint #security getting a boost from #AI and machine learning > scoop.it/topic/artifici…
#cybersecurity #infosec #endpointsecurity #tech #ArtificialIntelligence #ML #MachineLearning #ZeroTrust #leaders #leaders hip #CISO #CIO #CTO #security tools


Together, we help customers get more value out of their security and technology investments.
Learn more as Daniel Bernard, CBO of CrowdStrike, talks #hardwareassistedsecurity at the Cyber Resiliency Summit.
📺: dell.to/4cogR9l
#delltrustedworkspace #endpointsecurity


Simplified security settings management from within the Security portal is now generally available 🥳🥳🥳techcommunity.microsoft.com/t5/microsoft-d… #cybersecurity #infosec #endpointsecurity


The more barriers between cybercriminals and your systems, the less likely they are to pursue attacks like this ⬇️ Robust #EndpointSecurity stops man-in-the-middle attacks before they advance.
Microsoft Intune has been recognized as a Leader in The Forrester Wave™: Unified Endpoint Management, Q4 2023 report! Learn how Microsoft Intune simplifies management, reduces costs, and transforms experiences with AI and automation: msft.it/6014ize1O #EndpointSecurity

K7 Security has launched K7 Endpoint Security – Graphene which incorporates state-of-the-art patent-pending technology and proactive EDR developed by K7 to defeat the next generation of ransomware.
Request a trial at k7computing.com/in/business-us…
#endpointsecurity #cyber security #cyber


Vivek Ramachandran at SquareX shares his thoughts on #ZTNA in The Fast Mode’s latest #eBook ‘ #ZeroTrust in Action: Vendor Perspectives’.
Read the free eBook at
thefastmode.com/telecom-white-…
#trafficvisibility #networksecurity #cybersecurity #endpointsecurity Vivek Ramachandran

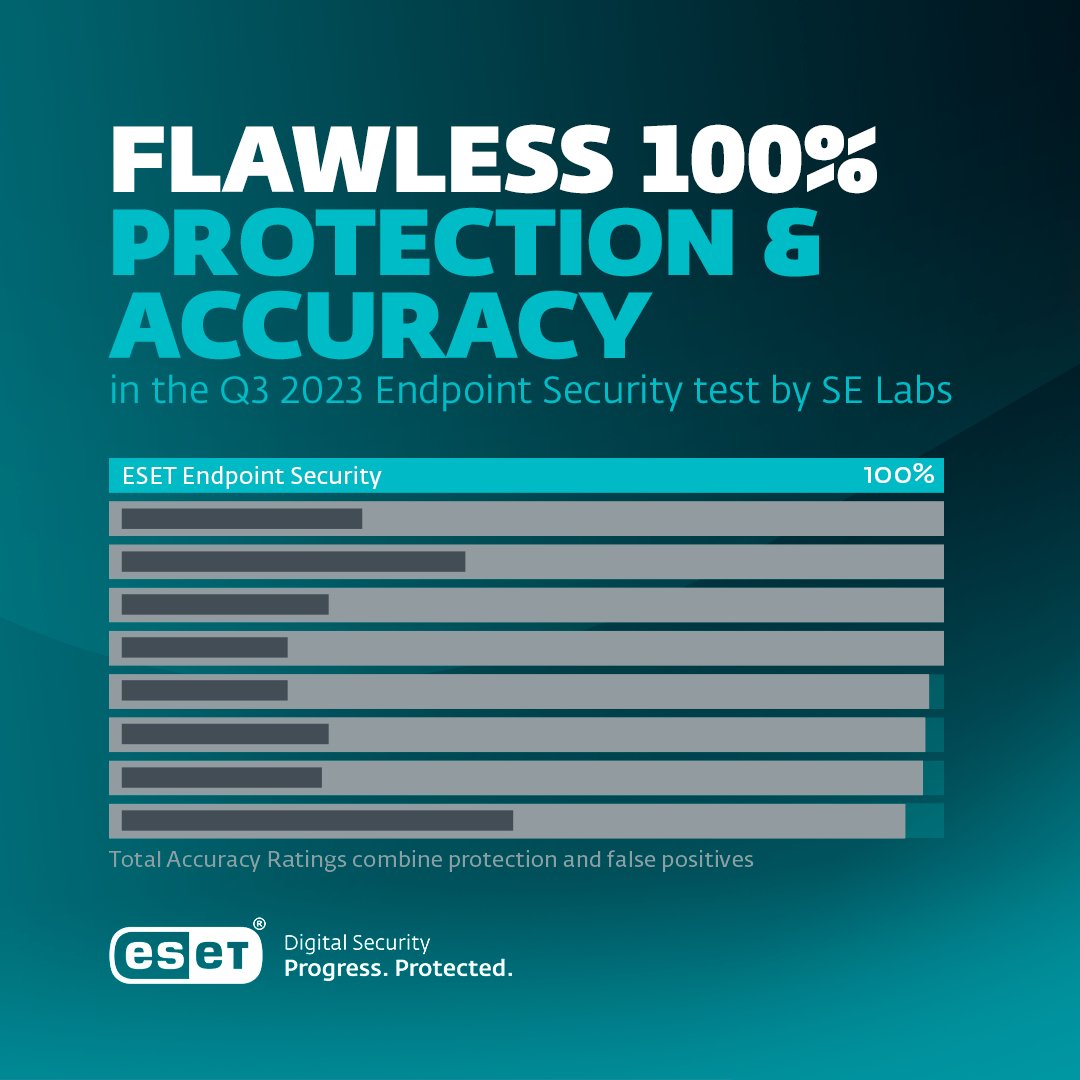
🏆 Exciting News! ESET clinches the AAA award in SE Labs Enterprise Endpoint Security test (2023 Q3), achieving flawless 100% protection & accuracy. Our commitment to top-notch protection and zero false positives stands strong.
#ESET #ProgressProtected #EndpointSecurity #SELabs
 's Twitter Profile Photo Martin Bengtsson [MVP](@mwbengtsson) 's Twitter Profile Photo](https://pbs.twimg.com/profile_images/709651255031947266/WEcdBCe9_200x200.jpg)
New blog post! How I stole my colleague’s OneDrive content and WiFi passwords using just a fake iPhone cable and PowerShell
imab.dk/how-i-stole-my…
#powershell #endpointsecurity #omg #redteam

Critical Trend Micro vulnerability exploited in the wild (CVE-2023-41179) - helpnetsecurity.com/2023/09/21/cve… - Trend Micro #ZeroDay #Vulnerability #TrendMicro #EndpointSecurity #ApexOne #WFBS #Cybersecurity News #InfoSec News #Cybersecurity #InfoSec


Detect 🔔
Investigate 🔎
Classify 🗃️
Manage ✅
This is how the Vodafone SOC keeps Villaggio Turistico Internazionale’s infrastructure secure. Read more in our case study: vdfn.biz/sOekI5
#Cybersecurity #EndpointSecurity #Phising


Endpoint #security getting a boost from #AI and machine learning
buff.ly/3MttOmI
VentureBeat LouisColumbus #cybersecurity #infosec #endpointsecurity #tech #ArtificialIntelligence #ML #MachineLearning #ZeroTrust #leaders #leaders hip #CISO #CIO #CTO #security tools


Top factors driving enterprise demand for new cybersecurity technology - helpnetsecurity.com/2023/06/08/cyb… - CCGroup ✊🏿🏳️🌈 Florie Lhuillier #ApplicationSecurity #EndpointSecurity #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurity News #SecurityNews

To combat these oversights by popular #endpointsecurity and SASE/SSE solutions, our enterprise solution offers organizations full visibility into the attack chain, enabling your company to effectively threat-hunt and identify similar attacks across their networks.
Vivek Ramachandran