
Security Best Practices for Serverless Applications
#AWS #Cloud #AWS Cloud #Serverless #Serverless OnAWS #Security #BestPractices #Security BestPractices #Lambda #AWS Lambda #API #API Gateway #AmazonAPIGateway #Microservices
youtube.com/watch?v=AV24RT…


Docker Image Security Best Practices #SecurityBestPractices #serverless
snyk.io/blog/10-docker…
Via HackerNews news.ycombinator.com/item?id=196030…


Ransomware Defense for Dummies explores best cyber security best practices to reduce risk.
bit.ly/32C7Kjv
Cisco Umbrella @Cisco #CiscoUmbrella #Ransomware #securitybestpractices

What you must know about CIS Benchmarks for AWS!
Learn about it in our latest blog post: clouddefense.ai/blog/you-must-…
#ClouddefenseAI #cisbenchmarks #awssecurity #cloudsecurity #cybersecurity #securitybestpractices #CloudDefense #compliance #PCIDSS #hipaa #soc2 #CSPM #CWPP #SAST


Never ever give your ID number, birth date or other pieces of confidential info to anyone over the phone, via SMS or email - no matter how innocent they may seem! #CyberSecurity AwarenessMonth #CyberSecurity #BeCyberAware #StayProtected #SecurityBestPractices #MODETrans



otalliance #DPD15 #securityBestPractices : 8. Web Application Firewalls/OWASP top 10
9. Wireless Device Management
10. Always on #SSL

Now that we’re set up to work remotely, check a few #securitybestpractices . Ensure your OS, office suite & security software are updated. If applicable, connect via your corp VPN. Change password of your ISP-provided Internet router (hint:Google), & use a home security router.


Read what Rom Hendler, CEO TRUSTIFI has to say about the Three Must-Haves For An Effective Security Compliance Plan.
#CyberSecurityCompliance #DataProtectionPlan #SecurityBestPractices #ComplianceFramework
#InformationSecurity
forbes.com/sites/forbeste…


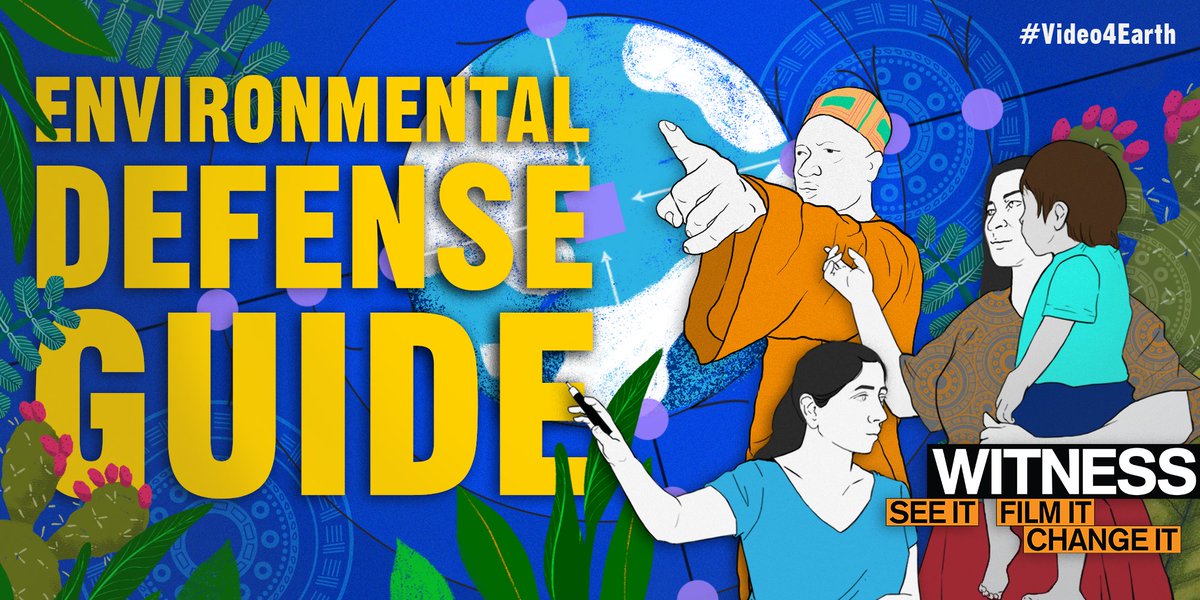
#Video4Earth
If possible to safely & ethically record, use video to document situations that are likely to result in mass injuries during & in the immediate aftermath of the incident.
The same steps used to document injuries to community members can be used to document harm to…

🛡️🔐Protect your #AzureAD privileged permissions with protected actions! Assign strong #ConditionalAccess policies to required permissions (7 ATM) and enforce policy at the time of protected actions. Learn more here 👉🏻learn.microsoft.com/en-us/azure/ac… #Cybersecurity #SecurityBestPractices


#Marqeta Developer Community - #SecurityBestPractices for #Fintech #Application #Development community.marqeta.com/t5/engineering…

Check out our latest blog post which dives into the recent testing we completed with The SecOps Group on LocalGov Drupal's cyber security.
👉 eu1.hubs.ly/H03yrJm0
Jamie Garrett, MD of Invuse, outlines #SecurityBestPractices and reveals the results!
#TheVoiceOfYourEndUsers


otalliance #DPD15 #securityBestPractices : 5. Email Authentication & DMARC - Inbound & outbound
6. Mobile Device Management
7. RT Monitoring

I wasn't aware of this helpful site. I learned that my email was compromised 9 times. Everybody needs to check if their personal information has been compromised.
#cybersecurity #securitybestpractices #privacy #phishing #datasecurity lnkd.in/ecsrA_x

Don't forget about security. Use best practices for authentication, authorization, and data protection to keep your software secure. 🔑 #securitybestpractices #authentication #100DaysOfCode #buildinpublic

8/11:
Protect your #Kubernetes secrets by encrypting them at rest
Enable encryption providers like Azure Key Vault or HashiCorp Vault to safeguard your secret dataEnsure only authorized personnel can access the encrypted secrets
#DataProtection #SecurityBestPractices #DevSecOps

Serverless Architectural Patterns and Best Practices buff.ly/2M7f0rN describes reusable #serverless patterns #securitybestpractices #serverless #architecture #AWS

I could not agree more! #cybersecurity #infosec #securitybestpractices twitter.com/sig_eu/status/…

'Life is too short to argue,
Just HACK him/her.'
😅
Berry Your Network 👨🏾💻🖤🌹
#cybersecurity #infosec #hacking #dataprotection #networksecurity #securityawareness #securitybestpractices #penetrationtesting
#vulnerabilitymanagement #socialengineering

Stay on top of security best practices. Regularly audit your backend codebase for vulnerabilities and apply necessary patches and updates. #SecurityBestPractices #BackendDevelopment
